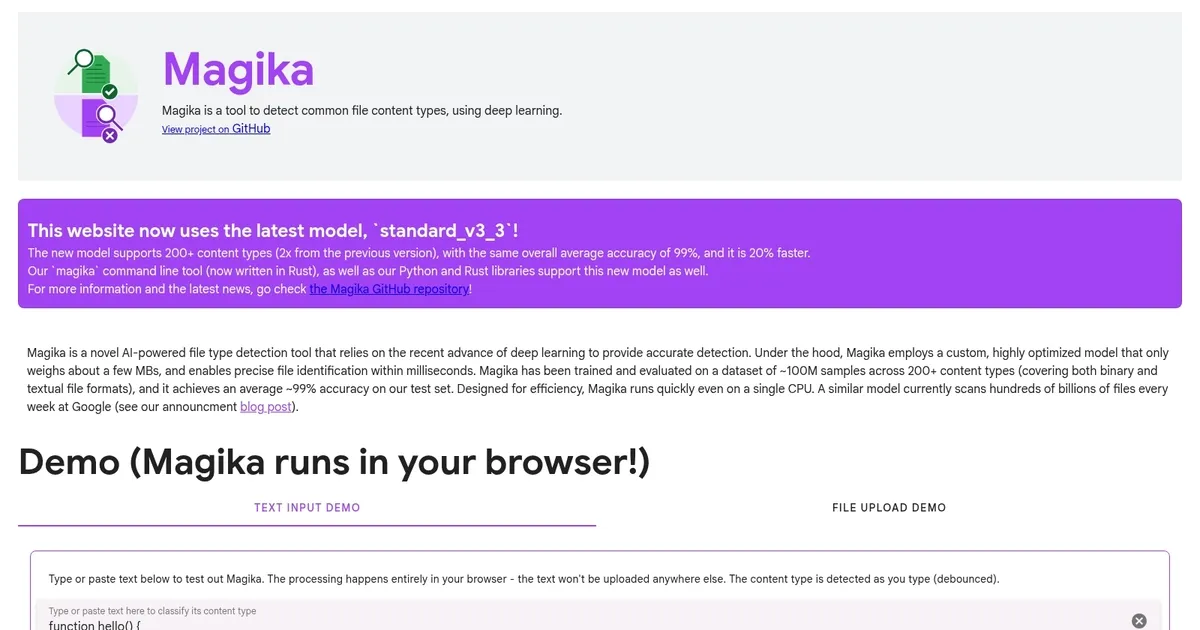
Magika by Google
Magika by Google is a state-of-the-art AI tool designed to quickly identify file types. Using advanced deep learning models, the tool can quickly recognize over 100 file types — including binary text formats — making it useful for enhancing cybersecurity systems by efficiently detecting and classifying files, even when they have been corrupted or encrypted.
As a Google service, Magika is obviously very precise. It features an average accuracy and recall rate of more than 99%, significantly outperforming traditional file identification methods based on manual search.
It’s an open-source tool, which means developers and researchers can look into the code and even make it better. Magika is available as a Python library, command-line tools, and there are also web demos you can test.
In a nutshell, Magica’s combination of speed, accuracy and open-source availability makes it valuable for improving file management and cybersecurity practices. By leveraging state-of-the-art AI, it provides a powerful tool for the wider tech community.
What are the key features? ⭐
- Deep learning for file detection: Magika utilizes advanced deep learning techniques to detect various file content types, thus improving detection accuracy over traditional methods.
- Comprehensive content type support: The tool supports many file types, making it versatile for different content detection needs.
- High accuracy: Magika boasts over 99% average accuracy in file type detection, ensuring reliable performance.
- Performance: It outperforms traditional file detection tools, offering faster and more efficient processing.
- Integrations: Designed to be easily integrated into existing systems, Magika provides a seamless enhancement to file detection capabilities.
Who is it for? 🤔
Examples of what you can use it for 💭
- Enhance malware detection by accurately identifying malicious file types
- Improve the organization of large datasets by correctly identifying file formats
- Assist in investigations by accurately detecting and categorizing file types in seized digital evidence
- Enhance email and web content filters by accurately identifying and managing file attachments
- Improve file handling features in applications by integrating precise file type detection.
Pros & Cons ⚖️
- Probably the best way to detect file types
- Could help cybersecurity efforts
- Different integration options
- Very specific tool, not needed for the majority of projects
FAQs 💬
Related tools ↙️
-
 Pineify
Generates error-free Pine Script indicators and strategies without coding
Pineify
Generates error-free Pine Script indicators and strategies without coding
-
 Oliv
Automates sales workflows with AI agents for deal tracking and coaching
Oliv
Automates sales workflows with AI agents for deal tracking and coaching
-
 Fina Money
Builds customizable AI-driven systems to track and optimize personal finances effortlessly
Fina Money
Builds customizable AI-driven systems to track and optimize personal finances effortlessly
-
 Upwork Uma
Streamlines freelance hiring with AI-powered skill assessments and job creation
Upwork Uma
Streamlines freelance hiring with AI-powered skill assessments and job creation
-
 ResuFit
Generates AI-tailored resumes, cover letters, and interview prep for job applications
ResuFit
Generates AI-tailored resumes, cover letters, and interview prep for job applications
-
 Pine Script Wizard
Generates custom Pine Script code for TradingView indicators and strategies from text descriptions
Pine Script Wizard
Generates custom Pine Script code for TradingView indicators and strategies from text descriptions